|
|
|
|
|
|
Go slow to go fast – planning, execution, and people are the cornerstones of the success of a good security strategy. Zero trust transformation requires a well-thought-out strategy and IT collaboration to realize the benefits throughout the journey.
|
|
|
| Jeff Lund, |
Global CISO - Global Information Security, Marsh McLennan |
 |
|
|
|
|
Preparing for a ‘Shields Up’ summer
Kyle Fiehler, Sr. Transformation Analyst
Current events present plenty of reasons CXOs will want to brush up on their incident response plans this summer.
Microsoft recently released a report outlining the expansion of Russian attacks against 128 organizations in 42 countries outside Ukraine. NGOs, allied nations and their corporations, as well as organizations providing material assistance to Ukraine are susceptible to being targeted by Russian cyber operations.
Meanwhile, the year's largest breach of PHI unfolded in the form of a series of attacks against U.S. eye care providers, and CISA warned that Log4j-related exploits are still being used to breach corporate networks.
It’s safe to say malicious actors aren’t taking a summer holiday. This drives home the importance of featured CXO Jeffrey Lund's advice on tabletop exercises. Practicing incident response plans with these drills can provide "vital intel needed to optimize reactions to potential incidents," he says.
|
|
|
Dispatches from Zenith Live 2022
Sharing CXO Program highlights
Zenith Live 2022 was a smash success as users from around the world descended on Resorts World Las Vegas from June 21 - 23. Zscaler unveiled new capabilities including
Posture Control for cloud workloads,
AI/ML enhancements for application segmentation, and an expanded
partnership with AWS.
The CXO REvolutionaries track also served up a full slate of executive-focused content. Conversations were animated, guests were inspiring, and featured speakers were knowledgeable.
To open, Zscaler CEO and Founder
Jay Chaudhry spoke with customers about zero trust as a
shared responsibility in today’s organizations. Zscaler leadership kept the event going when President
Amit Sinha, PhD;
Dhawal Sharma VP & GM, Product Management; and
Nathan Howe, VP, Emerging Technology & 5G took to the stage to talk about
the business enablement benefits of zero trust.
Field CTO
Pamela Kubiatowski appeared alongside CXO REvolutionary
Larry Biagini to discuss
lessons learned along their zero trust journeys. CISO - AMS
Bryan Green and guests shared advice for
thriving in a multi-cloud world. SVP, Product Management
Steve House and CISO and VP of Security Research and Operations
Deepen Desai also broke down
key ThreatLabz findings for executives.
If you missed any or all of the CXO Program presentations, you can catch up via the
Zenith Live 2022 on-demand page.
|
|
|
|
|
CXO REvolutionaries:
Podcast Center
Tune in to the latest voices from across our community of CIOs, CTOs, and CISOs for actionable advice and get inspired by some of the most passionate personalities in the industry.
|
|
 |
Zscaler CISO - AMS Bryan Green braved crowds and his own reservations to be on the scene at RSAC this year. Afterward, he joined Pam & Lisa to discuss popular topics – including identity and access management, securing cloud workloads, and managing third-party risk – and draw parallels between COVID-prevention best practices and zero trust strategies.
Listen now
|
 |
After the RSA showroom floor proved zero trust's popularity as a buzzword, how will its tenants be solidified and standardized to separate true adherents from charlatans? To find out, host Sean Cordero welcomes John Yeoh, global vice president of research at the Cloud Security Alliance, and Lauren Wise, senior director, global executive advisory at Zscaler to discuss the recently announced Zero Trust Advancement Center and its mission to become the vendor-agnostic industry "North Star" for the strategies and solutions that make up zero trust cybersecurity.
Listen now
|
|
|
|
Editor's Picks & Events
 |
In 2021, President Biden signed Executive Order 14028, “Improving the Nation’s Cybersecurity,” which mandates that all government agencies adopt a zero trust architecture. The National Institute of Standards and Technology (NIST) guides what this architecture should look like. However, many agencies are still searching for the best way to implement zero trust within their environment.
Read the complete key takeaways
|
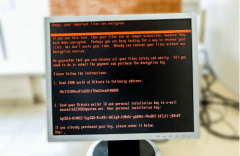 |
I recently wrote about my experience working as an IT architect for a Copenhagen-based multinational energy firm during the WannaCry ransomware attacks of May 2017. I didn’t know it at the time, but WannaCry was only a dress rehearsal for what turned out to be the single most destructive cyberattack of all time, one that would do some of its greatest damage less than five kilometers from where I then sat.
Read more about one CISO’s experience with NotPetya
|
 |
The swift evolution of IT infrastructures has made cybersecurity more challenging than ever for CISOs. They face a broader range of increasingly sophisticated threats aimed at a rapidly expanding and porous attack surface. That’s why Zscaler recently contributed to The CISOs Report, a new survey exploring CISOs' challenges, goals, and obstacles standing in their way.
Read key findings from the report
|
 |
Russia’s invasion of Ukraine over 100 days ago sent an earthquake rippling through the global landscape, and the ramifications have been profound. The war has made waves in the political, military, economic, and of course, cybersecurity spheres. Ukraine’s government agencies, banks, and other institutions have been struggling against a rising tide of cyberattacks executed in parallel with the invasion.
Learn how complacency can invite collateral damage
|
 |
Though cybersecurity is a swiftly evolving field, one principle remains constant: it’s often easier to fool people than to circumvent security tech. It’s also possible for attackers to orchestrate serious security breaches that involve no unauthorized access or subsequent technological manipulation at all. One successful technique for doing so is business email compromise (BEC).
Learn more about BEC and zero trust principles
|
|
|
|
|
|
|
|