|
|
|
|
|
|
Grit and resilience come as a package...if we are resilient, I don’t think we ever give up because people with resilience need only one thing-and that is hope.
|
|
|
| Dr. Malvika Iyer, |
Award-Winning Disability Rights Activist |
 |
|
|
|
|
Looking back on a month of honoring women
and their achievements
Christopher Jablonski, Editor in Chief
International Women's Day and Women's History Month were chances to celebrate the undeniable impact of women in the workplace and beyond. March demonstrated the range of their contributions to the CXO community.
Capping off our incredible Global IT Leadership Summit (more below), speaker Dr. Malvika Iyer moved and inspired her audience with her story of bravery, perseverance, and tenacity. Her work on opening doors for all women, in particular those with disabilities, after a horrific attack and subsequent life-threatening injuries is incredibly powerful.
Zscaler EVP, Customer Experience and Transformation Kavitha Mariappan demonstrated her leadership and support for professional women repeatedly. She advised on best practices for attracting, recruiting, and retaining women in IT, and her piece on mentoring spoke to how to advance the success of traditionally underrepresented groups within the industry.
Finally, Field CTO Lisa Lorenzin was one of several women IT leaders to speak with MeriTalk, a publication for federal CISOs and IT policymakers, about the benefits of a diverse workforce.
March may have been a month for formally celebrating women, but their contributions move us forward daily. The above stories are just a few examples of that.
Finally, in the spirit of inspiring events, we hope you’ll join us for a Zscaler Virtual CXO Summit this April. We'll be bringing together industry leaders from around the globe to share expertise from transformational careers, as well as discussing the new CSA Zero Trust Advancement Center and its mission to accelerate zero trust through education. Be sure to register for the event in your geo here.
|
|
|
From the office of the CISO
Higher ed gets an 'F' for ransomware protection: how the industry must evolve
Bryan Green, CISO Americas
It’s human nature to go after the low-hanging fruit first, threat actors are no different. And from the standpoint of cybercriminals, colleges and universities are exceptionally vulnerable targets for ransomware attacks.
Why? Partly, it’s because these institutions often have the financial resources to pay high ransoms — $1.14 million from the University of California, San Francisco, and $457K from the University of Utah serve as two recent examples.
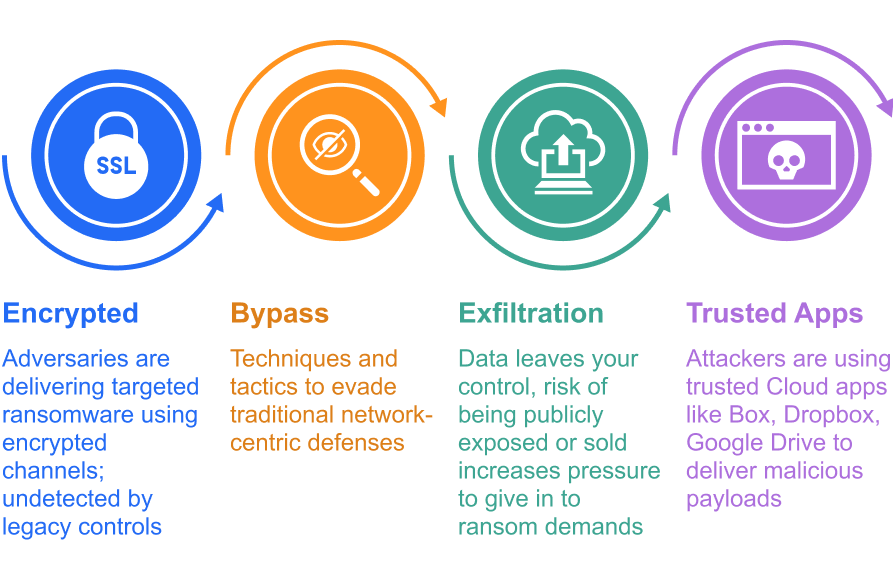
University networks are especially attractive to attackers, as their underlying security architectures are often representative of liberal academic cultural values and typically lag behind enterprises in sophistication and efficacy.
|
|
|
|
|
CXO REvolutionaries:
Podcast Center
Tune in to the latest voices from across our community of CIOs, CTOs, and CISOs for actionable advice and get inspired by some of the most passionate personalities in the industry.
|
|
 |
On this episode, our guest Misha Kuperman, Zscaler SVP cloud operations and ecosystem, returns for an update on the Zscaler cloud. He shares a platform review, thoughts on current issues like supply chain threats and geopolitical risks, and the implications of the “Cold War” between the West and China – which has been exacerbated by the FCC's decision to revoke Chinese telecoms' authorization to operate in the US, a decision it made citing national security.
Listen now
|
 |
Once you have a zero trust architecture in place, it can enable cybersecurity capabilities that will be commonplace in the future. In this episode, host Phil Armstrong welcomes guests Maneesh Sahu, director, OT network and security transformation, Zscaler, and Bil Harmer, operating partner, Craft Ventures. They discuss securing the supply chain by minimizing supplier risk and integrating third-party identities, advances and challenges in device identity, IoT security, and more.
Listen now
|
|
|
|
Editor's Picks & Events
 |
Moving to zero trust requires a willingness to change and a commitment to future-proofed investment. Join us for this event to learn from corporate security and risk-management innovators about how to kickstart or complete your journey.
Register now
|
 |
On March 1, 2022, we hosted the unforgettable inaugural Zscaler Global IT Leadership Summit. Zscaler CEO and Founder Jay Chaudhry was joined by an incredible lineup of IT leaders including Microsoft CEO and Chairman Satya Nadella and top IT executives from Microsoft, Siemens, Hitachi, VF Corporation, and Zscaler. View the recording or read the recap to hear about their amazing stories of digital transformation.
Learn lessons from these top IT executives here
|
 |
This March the Cloud Security Alliance (CSA) announced the creation of its CSA Zero Trust Advancement Center, meant to be the industry standard program for zero trust education. Zscaler is proud to join Okta and CrowdStike as a founding partner of CSA's new education initiative as it promotes zero trust principles without spin or bias.
Read more about the CSA Zero Trust Advancement Center
|
 |
In the early days of cloud adoption, enterprises were slow to entrust their data to off-site servers owned by outside entities. First, relationships had to be built step by step. Today, zero trust principles require an even greater level of interpersonal trust. In this article, Rohit Adlakha and Sudip Banerjee, two IT executives with more than 40 years of experience share advice on building relationships with potential partners.
Get tips for positioning trust with trust here
|
 |
Mergers and acquisitions were big business in 2021, a $5.9 trillion market according to Bain & Company. Here Stephen Singh, VP, outsourced projects and M&A IT integration, explains how zero trust principles simplify the M&A processes by shortening TSAs, easing the adoption of cloud services, and helping organizations achieve compliance.
See how zero trust accelerates success in mergers, acquisitions, and divestitures
|
 |
Part 3 of the SSE solution series, adopted from the eBook The 7 Pitfalls to Avoid when Selecting an SSE Solution, outlines how to choose SSL/TLS inspection of traffic at scale. Catch up on it and other chapters in the series here.
View part 3 in the SSE solution series
|
|
|
|
|
|
|
|
|